-

Software Design & Development
WTI builds smarter applications to deliver core functionalities and powerful agility. Our software is developed with the specific requirements of our customers in mind, adapting to their needs. The result is a product that creates a competitive advantage for our customers.
Read More -

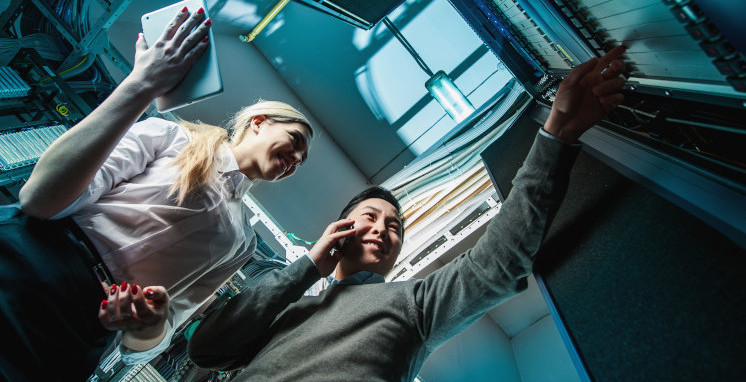
Network & CyberSecurity
Cyber threats have changed our world, making online security and defense a top priority for organizations of all shapes and sizes. Following industry best practices, WTI protects government and military assets and defends businesses.
Read More -

AI & MACHINE LEARNING
AI and machine learning services provide advanced solutions for task automation, data analysis and predictive analytics. Our expert team delivers tailored AI & ML services that elevate your business, ensuring seamless innovation, efficiency, intelligent systems and sustainable computational models.
Read More -

Planning & Budgeting
We work with our customers’ financial offices to implement a robust, 3-step budgeting, planning and forecasting (BP&F) process that helps determine and detail long- and short-term financial obligations and goals.
Read More -

Managed Services
As a trusted IT solutions provider and partner for over 15 years, we take the IT management load off our customers’ daily routine. With their IT responsibilities delegated to us, customers not only have fewer headaches, but they tap into a pool of powerful resources as well.
Read More